At the firewall level, your approach to filtering should be more fine-grained. As with your border router, first and foremost it is important to lock down access to the firewall itself. These include enhanced security, intrusion prevention, network segmentation, and application control. They safeguard sensitive information, maintain network performance, offer detailed control over network traffic, 192.168.0 and assist in ensuring regulatory compliance. Modern firewalls provide application control, allowing you to manage how applications are used on your network.
- You have a different IP address for internal purposes, such as identifying your devices within a home network or inside a business office.
- To understand how an IP address works, it’s essential to grasp the basic mechanism of data transmission over the internet.
- Also, after a reboot NetworkManager manages assignments for “activating” those zones.
- The distinct advantage is its ability to obscure internal network structures and enhance security protocols by preventing direct communication between internal clients and external servers.
- CIDR allows us more control over addressing continuous blocks of IP addresses.
- In terms of security, dynamic IP addresses can be more secure and offer more anonymity.
Routers/modems that allow multiple computers to be connected–either over ethernet or WiFi–will use NAT to do this sharing. Sometimes, older routers offer UPnP support that may not work with new applications.
H3: Method 3: Cloud Storage and Services
To strengthen your IP address reputation management, use a VPN to conceal your IP address when browsing the internet. Without a VPN, websites can gather information whenever you visit them, which includes your session, browsing habits, and the links you click on. In addition, your location can be tracked via the IP address even when the GPS or location services are turned off. Dedicated IP addresses are typically available as an additional service from your hosting provider or ISP. At Hostinger, you can get a dedicated IP address for free by purchasing our Cloud hosting or VPS hosting plans. These IP addresses are cost-effective, as many websites can share the same web servers and resources.
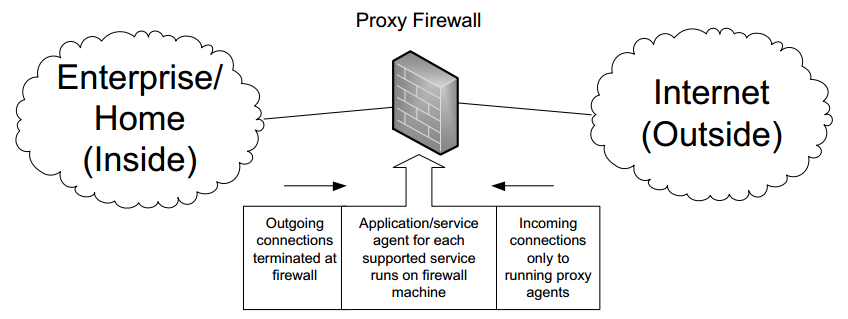
Devices that track state ascertain which states are safe and which pose threats. With a network zone structure established, it is also important to establish a corresponding IP address structure that assigns zones to firewall interfaces and subinterfaces. Proper firewall configuration is essential, as default features may not provide maximum protection against a cyberattack. As the primary defense line against attacks, perimeter firewalls employ different techniques to control traffic between an organization’s network and untrusted networks. There are several types of firewalls, each with its unique features, advantages, and disadvantages. In this article, we will explore the different types of firewalls and their use cases, and help you determine which is best suited for your specific situation. A few of these filters can also edit messages, like deactivating the malicious links before users actually click on them.